What is an Access Control System ?
An Access Control System is a comprehensive security solution designed to manage and regulate entry to physical spaces, ensuring that only authorized individuals can access certain areas. These systems are integral to safeguarding sensitive locations such as offices, industrial facilities, government buildings, and even residential properties. By utilizing various identification methods like keycards, biometrics, and PINs, access control systems enhance security, mitigate risks, and protect valuable assets.
With advancements in technology, modern access control systems offer real-time monitoring, detailed access logs, and seamless integration with other security measures like surveillance cameras and alarm systems. These features make it easier to manage who enters and exits a location, both on-site and remotely via cloud-based platforms. As the need for robust security solutions continues to grow, access control systems have become a fundamental component of both residential and commercial security strategies.
Key Components of an Access Control System
To understand the workings of an access control system, it is essential to look at its primary components: entry points (doors, gates), access credentials, control panels, and management software. Each of these elements plays a critical role in how the system authenticates users and grants or denies entry.
Each of these devices works together to create a robust, seamless access control system that can be tailored to the specific security needs of any organization or residence.
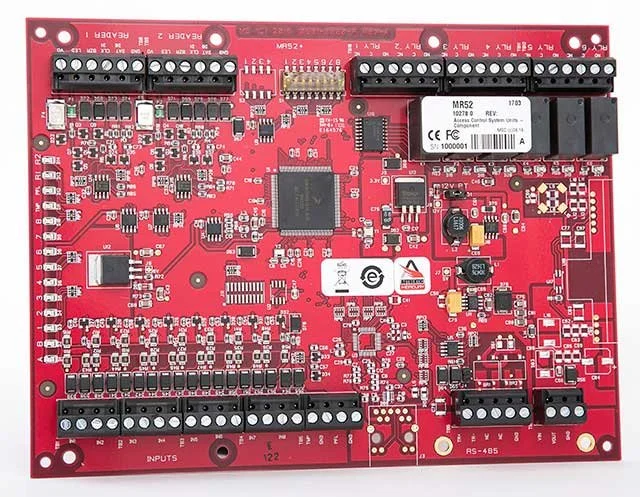
1. Controllers
A controller is a key component in access control systems, managing the flow of information between entry points (doors, gates) and devices like card readers, keypads, and biometric scanners. It processes credentials to grant or deny access based on pre-set permissions.
Widely used in offices, industrial sites, and secured facilities, door controllers enable centralized management of multiple entry points. They integrate with other security systems, like surveillance cameras and alarms, and often offer network capabilities for remote control and real-time monitoring. By storing access logs and tracking user activity, they ensure efficient operation in large or complex access control setups.
2. Card Readers
Card readers are key devices in access control systems, verifying credentials from keycards, proximity cards, or fobs to grant or deny access to secure areas.
Commonly found in offices, government buildings, and residential complexes, they provide fast, contactless entry while enhancing security. Card readers support various technologies like RFID, magnetic stripe, and smart cards, ensuring wide compatibility.
Modern card readers often integrate with networked systems for real-time access logs, remote management, and additional security features, such as surveillance integration. Their durable, tamper-resistant design ensures reliable performance indoors and outdoors.
3. Keypads
Keypads are common access control devices that require users to enter a Personal Identification Number (PIN) for entry to secured areas. Frequently used in offices, warehouses, and residential buildings, they provide a simple, effective way to restrict access without physical cards or fobs.
They can be used alone or combined with other methods, such as card readers or biometric scanners, for added security. Keypads are durable, easy to install, and ideal for locations needing frequent user access.
4. Magnetic Locks
Magnetic locks, or maglocks, use an electromagnet to secure doors until access is granted, making them popular in offices, retail stores, and high-security facilities. They integrate seamlessly with access control systems like card readers, keypads, and biometric scanners.
Known for their fail-safe design, maglocks unlock automatically during power outages, ensuring safe evacuation in emergencies. Easy to install and low-maintenance, they are suitable for both indoor and outdoor use. With no moving parts, maglocks are highly durable and can be integrated into automated security systems, offering robust security and versatility in various environments.
5. Electric Strikes
Electric strikes are locking devices used in access control systems that secure doors while allowing remote or controlled access. They release the door latch when activated by devices like card readers, keypads, or intercoms, enabling authorized entry without a traditional key. Commonly found in offices, apartment complexes, and high-security areas, electric strikes are versatile and integrate easily with various access methods.
Available in fail-secure (locking during power loss) and fail-safe (unlocking during power loss) types, they are adaptable for both security and emergency evacuation needs. Compatible with a wide range of doors and lock types, electric strikes provide reliable performance, making them a key component in modern access control systems for high-traffic areas.
6. Door Contacts
Door contacts are vital security sensors used in access control and alarm systems to detect whether a door is open or closed. These small magnetic devices, installed on doors and frames, trigger alerts if a door is opened without authorization. Widely used in offices, homes, warehouses, and high-security facilities, they provide real-time monitoring and are crucial for intrusion detection.
Integrated into access control systems, door contacts ensure compliance with security protocols, alerting users to unauthorized access or doors left ajar. They can also be connected to alarms or automated notifications for immediate responses to breaches. Durable and easy to install, door contacts are an effective tool for enhancing security in both indoor and outdoor environments.
7. Request to Exit (REX)
Request to Exit (REX) devices are components of access control systems that allow users to exit secured areas without re-authenticating their identity. Commonly installed near doors in offices, warehouses, and secure facilities, REX devices come in forms like motion sensors, push buttons, or touch-sensitive plates.
These devices simplify the exit process while maintaining security, ensuring only authorized personnel can exit through controlled points. Motion sensor REX devices unlock automatically when movement is detected, while push-button models require a physical press to open the door.
Many REX devices integrate with alarms to log exits and monitor for unauthorized use, enhancing security. Their ease of use and reliable performance make REX devices essential in ensuring both security and convenience in access-controlled environments.
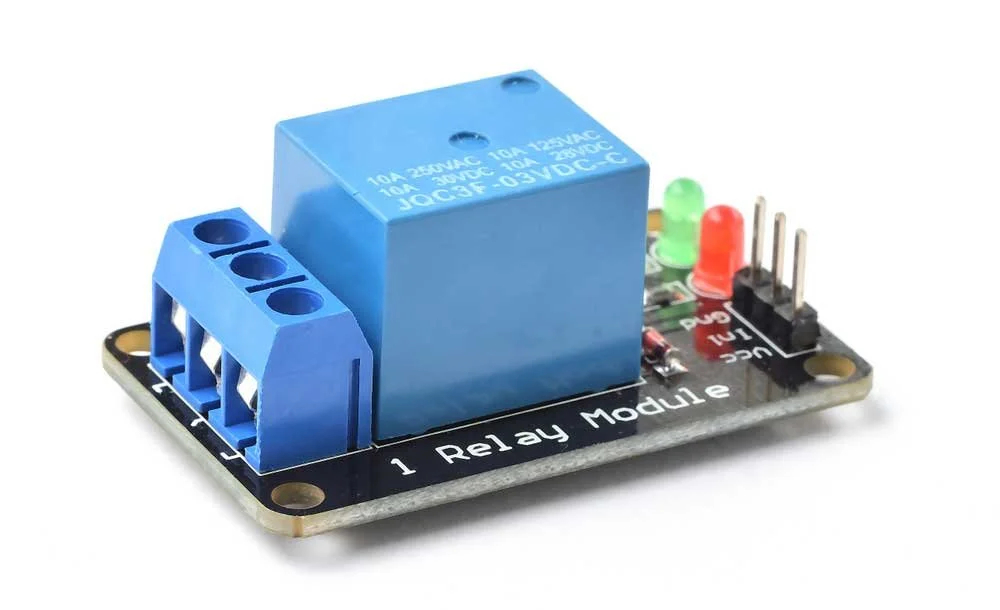
8. Relay Modules
A relay module is an essential part of access control systems, linking control panels with locking devices like electric strikes, magnetic locks, or alarms. It uses low-power signals from readers or keypads to activate high-power locks, ensuring secure access when granted.
Used in commercial buildings, industrial sites, and smart homes, relay modules enhance system flexibility by supporting multiple devices and integrating access points. They also protect sensitive components by isolating electrical circuits, offering safety and reliability. Easy to install and versatile, relay modules are critical for seamless operation in modern access control systems.
9. Servers
Servers are the backbone of access control systems, managing and storing data from devices like card readers, keypads, and biometric scanners. They allow administrators to monitor and control access points in real time. Depending on the system's complexity, servers can range from a small desktop for single locations to a farm of servers managing multiple sites and large data volumes.
Servers handle tasks such as storing credentials, generating access logs, and integrating with security systems like surveillance cameras. Whether cloud-based or on-premise, servers offer scalability and reliability, ensuring smooth operation for both small setups and large enterprises, making them vital for maintaining robust security.
Conclusion
Access control systems are essential in today’s security landscape, offering a wide range of solutions for managing and restricting entry to secure areas. With components like card readers, keypads, magnetic locks, door controllers, and servers, these systems provide a comprehensive approach to safeguarding homes, businesses, and high-security facilities. From small, standalone setups to large, server-driven operations, access control systems can be tailored to meet the specific needs of any environment, ensuring both convenience and robust protection.
As technology continues to evolve, modern access control systems are becoming more sophisticated, integrating features like real-time monitoring, remote management, and seamless integration with other security measures such as surveillance cameras and alarm systems. This ensures a holistic approach to security, making access control a vital element in any organization’s overall safety strategy.
Tailored Solutions by iSECUR
Access control systems can be fully customized to suit your unique security needs, providing the perfect solution for homes, businesses, or large facilities. Our team of experts will assess your site to design and implement a system that ensures optimal security and streamlined access management. Whether you require a simple setup with keypads or card readers or a more advanced solution with biometric authentication and remote monitoring, we will deliver a tailored system that enhances security while maintaining convenience and control.
Enhance Your Security With Us!
Book your free on-site consultation today! Our certified security experts will visit your property, assess your unique needs, and recommend the best security solutions tailored to you. We'll provide professional guidance to ensure your home or business is fully protected with a system that fits both your budget and requirements.